Introduction to Business Security
In the contemporary business environment, security is a critical concern for organizations of all sizes. Protecting assets, sensitive information, and ensuring the safety of employees and customers are paramount objectives for any business. Business security encompasses a range of practices and tools designed to shield businesses from various threats, including physical break-ins, vandalism, theft, and even cyber-attacks.
Importance of Business Security
Ensuring business security is not merely about preventing loss or damage to physical property. It also involves mitigating risks related to data breaches, maintaining the integrity of a company’s reputation, and complying with regulatory requirements. The significance of securing business premises can be summarized as follows:
- Asset Protection: Preventing unauthorized access to buildings, equipment, and other valuable assets.
- Employee Safety: Ensuring a secure working environment for employees.
- Data Security: Safeguarding sensitive information from theft or damage.
- Business Continuity: Minimizing disruptions that can be caused by security breaches.
- Regulatory Compliance: Adhering to industry standards and legal requirements.
Components of Business Security
A comprehensive business security strategy typically includes multiple layers and components to address various risks. These components can be broadly categorized as follows:
| Component | Description |
|---|---|
| Physical Security | Measures such as locks, barriers, surveillance cameras, and alarm systems to prevent unauthorized physical access. |
| Information Security | Practices and technologies like firewalls, encryption, and secure access protocols to protect digital data. |
| Personnel Security | Policies and procedures for hiring, training, and monitoring employees to reduce internal risks. |
| Procedural Security | Operational protocols and emergency response plans to ensure readiness and proper action during security incidents. |
Integrating these components effectively requires a thorough understanding of the potential threats specific to each business and tailoring security measures accordingly.
Role of Alarm Systems
Alarm systems play a crucial role in the overall security strategy of a business. They serve as both a deterrent and a responsive measure to potential security breaches. By alerting business owners and security personnel of unauthorized access or unusual activities, alarm systems help in promptly addressing threats before significant damage occurs.
In summary, business security is an essential aspect of modern organizational management, blending various strategies and technologies to safeguard assets, personnel, and information. Alarm systems are a cornerstone of physical security within this broader framework, providing necessary alerts that can avert potential threats and enhance safety.
Historical Evolution of Alarm Systems
The concept of alarm systems can be traced back to ancient civilizations where rudimentary security measures were employed to protect property and goods. However, the history of modern alarm systems began in the mid-19th century with significant technological advancements that laid the groundwork for contemporary security solutions.
Early Beginnings
The first significant development in alarm systems came in 1853 when Augustus Pope patented an electro-magnetic alarm system. This early design used a simple circuit to alert building occupants of a possible intrusion. Edwin Holmes later bought Pope’s patent and founded the first company dedicated to manufacturing and installing electrical alarm systems for businesses and homes.
Advancements in the 20th Century
The 20th century saw substantial progress in alarm technologies. The introduction of telephone-based alarm systems in the 1920s allowed for a broader diffusion and real-time notifications. In the 1940s and 1950s, advancements in control panels and detection technologies provided more reliable and user-friendly systems.
Emergence of Automated Systems
During the 1970s and 1980s, the use of microprocessors in alarm systems revolutionized the industry. Automated systems emerged, which could monitor multiple zones and offer more sophisticated features such as remote arming and disarming.
Integration with Digital and Wireless Technologies
The late 20th and early 21st centuries have been marked by the integration of digital and wireless technologies. Modern alarm systems now use internet protocols, mobile applications, and wireless sensors, enabling real-time monitoring and control from virtually anywhere.
Notable Milestones
Several key milestones marked the development of alarm systems throughout history:
- 1853: Patenting of the first electro-magnetic alarm system by Augustus Pope.
- 1877: Edwin Holmes establishes the first professional alarm company.
- 1920s: Introduction of telephone-based alarm systems.
- 1980s: Integration of microprocessor technology in alarm systems.
- 2000s: Adoption of digital and wireless technologies.
Evolution Summary Table
| Period | Key Developments |
|---|---|
| Mid-19th Century | Invention of electro-magnetic alarm systems |
| 1920s | Telephone-based alarm systems |
| 1970s-1980s | Microprocessors and automated systems |
| 1990s-2000s | Digital and wireless integration |
Types of Alarm Systems and Their Features
Types of Alarm Systems and Their Features
Businesses today have access to a range of alarm systems designed to enhance security. Each type of alarm system offers various features and benefits that cater to different security needs.
Intrusion Alarm Systems
Intrusion alarm systems are designed to detect unauthorized entry into a building or area. These systems employ a range of sensors, including door and window sensors, motion detectors, and glass break detectors.
- Door and Window Sensors: These sensors monitor the opening and closing of doors and windows. When a door or window is opened unexpectedly, the sensor triggers the alarm.
- Motion Detectors: These devices use infrared technology to detect movement within a specified area. When motion is detected, the alarm is activated.
- Glass Break Detectors: These sensors detect the sound of breaking glass and trigger the alarm if such a sound is detected.
Fire Alarm Systems
Fire alarm systems are essential for detecting and alerting occupants to the presence of fire or smoke. These systems help in preventing the spread of fire and ensuring timely evacuation.
- Smoke Detectors: Smoke detectors sense the presence of smoke and activate the alarm. There are two main types of smoke detectors: ionization and photoelectric.
- Heat Detectors: These detectors respond to an increase in temperature and trigger the alarm when a predetermined threshold is reached.
- Manual Pull Stations: These devices allow occupants to manually activate the fire alarm in case of an emergency.
Video Surveillance Systems
Video surveillance systems involve the use of cameras to monitor and record activities within and around a business premises. Modern systems often include advanced features such as remote viewing and motion-activated recording.
- Closed-Circuit Television (CCTV): CCTV systems use video cameras to transmit a signal to a specific place, on a limited set of monitors. This is a widely used component of modern security systems.
- IP Cameras: Internet Protocol (IP) cameras send and receive data via a computer network and the internet. These cameras offer high-resolution video and are often used for remote monitoring.
Access Control Systems
Access control systems restrict entry to authorized personnel only. These systems help in managing who enters or exits a building or specific areas within a building.
- Key Card Systems: Key cards are issued to employees, which they can use to access secured areas by swiping or tapping the card on a reader.
- Biometric Systems: These systems use unique biological characteristics, such as fingerprints or retinal scans, to authenticate individuals.
Each of these alarm systems plays a crucial role in safeguarding businesses from different threats. By understanding their features, businesses can choose the most appropriate alarm system to meet their security needs effectively.
Effectiveness of Alarm Systems in Deterrence and Detection
Effectiveness of alarm systems in both deterrence and detection has been a major topic of study in the domain of business security. Numerous empirical studies have demonstrated that alarm systems serve as a robust preventive measure against criminal activities.
Deterrence
Alarm systems have proven to be effective deterrents. According to a study conducted by the University of North Carolina at Charlotte, approximately 60% of convicted burglars indicated that the presence of an alarm system would compel them to seek an alternative target. The mere visibility of a security system can significantly reduce the likelihood of a break-in.
- Burglar alarms reduce crime by 60% in buildings that have them installed.
- Presence of alarm signage further minimizes risk as reported by the National Council for Home Safety and Security.
Detection
Detection capabilities of alarm systems have also shown substantial benefits. Systems equipped with motion sensors, door/window sensors, and glass break detectors ensure that unauthorized activities are swiftly identified and addressed. The FBI reports that alarm systems increase the chances of detaining criminals by 30% when they trigger immediate police dispatch.
Below is a table that summarizes key findings from various research on the effect of alarm systems:
| Effect | Research Findings |
|---|---|
| Reduction in Break-ins | 60% reduction as per the University of North Carolina study |
| Criminal Detention Rate | 30% increase in detentions according to the FBI statistics |
These findings collectively highlight the dual role of alarm systems in both deterring potential criminals and aiding in the detection of unauthorized activities. By mitigating security risks, alarm systems play a crucial role in maintaining business security and protecting assets.
Integration of Alarm Systems with Modern Technologies
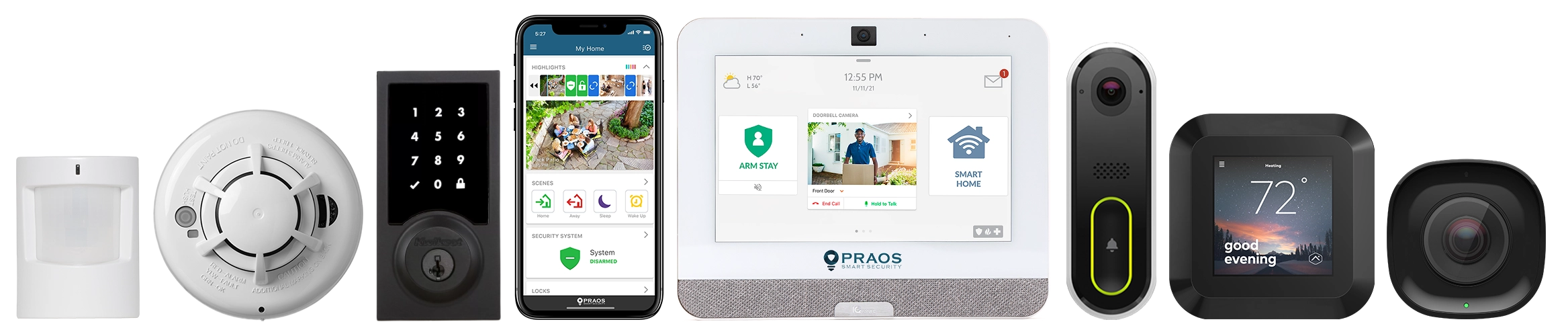
The integration of alarm systems with modern technologies has significantly enhanced the capabilities of business security setups. As technology advances, the synergy between alarm systems and other sophisticated security technologies becomes pivotal in ensuring comprehensive protection. This chapter delves into how contemporary technological advancements interlace with traditional alarm systems to provide improved security solutions for businesses.
Smart Sensors and IoT Integration
The Internet of Things (IoT) has enabled alarm systems to become more responsive and interconnected. Smart sensors are pivotal in this integration, offering real-time monitoring and data collection capabilities.
- Real-Time Monitoring: Smart sensors monitor environmental changes and trigger alarms when anomalies are detected.
- Data Collection: Sensors collect data that can be analyzed for patterns, helping businesses identify potential security threats proactively.
- Interconnectivity: IoT devices communicate with each other, creating an integrated security network that enhances situational awareness and response times.
Cloud Computing and Data Analytics
Cloud computing and data analytics play crucial roles in modern alarm systems. These technologies allow for the storage, processing, and analysis of vast amounts of security data.
- Scalability: Cloud-based systems can scale easily to accommodate growing business needs without significant infrastructure investments.
- Remote Access: Businesses can access their security systems remotely, allowing for round-the-clock monitoring and management.
- Predictive Analytics: Data analytics provide insights and predictive models that help in identifying and mitigating potential threats before they occur.
Integration with Artificial Intelligence (AI)
AI is increasingly being incorporated into alarm systems, providing enhanced capabilities such as pattern recognition, anomaly detection, and automated responses.
- Pattern Recognition: AI algorithms analyze data to recognize patterns of normal and suspicious activities.
- Anomaly Detection: AI identifies irregularities that human operators might miss, allowing for quicker responses to potential threats.
- Automated Responses: AI-driven systems can automatically trigger specific actions or alerts, enhancing the overall responsiveness of the security system.
Enhanced Video Surveillance
Modern alarm systems often integrate with advanced video surveillance technologies, providing visual verification and documentation of events.
- High-Resolution Cameras: Enhanced imaging quality aids in the clear capture of incidents, facilitating identification and evidence gathering.
- Motion Detection: Integrated motion sensors can activate cameras and recording devices, ensuring that relevant footage is captured.
- Remote Viewing: Video feeds can be accessed remotely, allowing security personnel to monitor premises in real time from any location.
Biometric Systems
Biometric technologies are increasingly being used in conjunction with alarm systems to provide robust access control and authentication.
- Fingerprint Scanners: These are used to verify identities with a high degree of accuracy, reducing the risk of unauthorized access.
- Facial Recognition: AI-powered facial recognition systems offer non-intrusive and highly secure methods of human identification.
- Iris Scanning: Iris scanners provide an additional layer of security, particularly suited for high-security areas.
Table: Benefits of Integrating Modern Technologies with Alarm Systems
| Technology | Benefit |
|---|---|
| IoT Smart Sensors | Real-time monitoring and interconnectivity |
| Cloud Computing | Scalability and remote access |
| AI | Pattern recognition and automated responses |
| Video Surveillance | Enhanced imaging and remote viewing |
| Biometric Systems | Robust access control and authentication |
In conclusion, the integration of alarm systems with modern technologies has greatly bolstered the efficiency and effectiveness of business security. By leveraging advancements in IoT, cloud computing, AI, video surveillance, and biometric systems, businesses can achieve comprehensive and proactive security management.
Future Trends in Alarm Systems and Business Security
The future of alarm systems in business security is poised for significant advancements. As technology continues to evolve, several key trends are expected to shape the landscape of business security through enhanced alarm systems.
Artificial Intelligence and Machine Learning
One of the most transformative trends is the integration of artificial intelligence (AI) and machine learning (ML) into alarm systems. These technologies enable alarm systems to become smarter and more adaptive. AI can analyze vast amounts of data to identify patterns and predict potential threats, improving the accuracy and efficiency of these systems. ML algorithms allow alarm systems to learn from past incidents and enhance their detection capabilities over time.
Internet of Things (IoT) Integration
The Internet of Things (IoT) is another significant trend influencing the future of alarm systems. IoT-enabled devices can seamlessly communicate with each other, creating a more integrated and responsive security ecosystem. Businesses can benefit from IoT by connecting various security components, such as cameras, sensors, and access control systems, to centralize monitoring and control. This connectivity allows for real-time data exchange and alerts, enhancing the overall security posture.
Cloud-Based Solutions
Cloud technology is increasingly being adopted for alarm systems, offering numerous advantages. Cloud-based alarm systems provide enhanced scalability, allowing businesses to expand their security infrastructure without substantial investment in hardware. Additionally, cloud solutions enable remote management and access to real-time data from anywhere, offering greater flexibility for business owners and security personnel. The use of the cloud also ensures that data is backed up and protected against physical damage or theft.
Enhanced Cybersecurity Measures
As alarm systems become more interconnected and reliant on digital technologies, cybersecurity becomes a critical concern. The future will see alarm systems incorporating more robust cybersecurity measures to prevent unauthorized access and protect sensitive data. This includes the use of encryption, two-factor authentication, and regular software updates to address potential vulnerabilities.
Biometric Authentication
Biometric technology is increasingly being integrated into alarm systems to enhance security and reduce the likelihood of unauthorized access. Biometric authentication methods such as fingerprint recognition, facial recognition, and retina scans offer a higher level of accuracy and security compared to traditional methods like passwords or keycards. These technologies can be used to control access to restricted areas and to ensure that only authorized personnel can disarm or interact with the alarm system.
Environmental Sustainability
Sustainability is also becoming a focus in the development of future alarm systems. Manufacturers are exploring ways to create more environmentally friendly security solutions by using energy-efficient components and exploring renewable energy sources like solar power. These efforts not only help reduce the environmental impact but also align with the growing trend of corporate social responsibility among businesses.
In summary, the future of alarm systems in business security will be marked by greater intelligence, connectivity, scalability, cybersecurity, biometric authentication, and sustainability. These advancements promise to provide businesses with more robust, efficient, and secure alarm systems to protect their assets and operations.